Most mobile phones in the world (also called cell phones, or hand phones) use the GSM network, and GSM generally uses an encryption protocol called A5.
 A5 encryption was always a weak design but the equipment to decode it used to cost between US$70,000 and US$500,000 so it wasn’t very common.
A5 encryption was always a weak design but the equipment to decode it used to cost between US$70,000 and US$500,000 so it wasn’t very common.
Now some new research shows it can be cracked with around US$1000 of equipment. This makes it accessible to most businesses and individuals. It’s still theoretical though it won’t be long until anyone can download the software required to do it.
What does this mean to phone users?
Conversations carried out over mobile phones should not be considered secure. If the technology exists for competitors to sit outside an office and listen in on calls then you should change how you carry out business.
Apart from this new research on cracking the encryption there’s another method that has existed since phone networks began operation. All mobile phone carriers have the ability to record conversations for law enforcement purposes. They just have to press some buttons on their computer and your conversations get recorded. So you shouldn’t be sharing trade secrets on the phone anyway.
And now’s a good time to mention that SMS messages have never been secure. Most GSM networks keep a log of all SMS messages and this information is available to law enforcement agencies (or to anyone corrupt at the phone companies or to anyone that hacks into a phone company’s network).
Some articles to read if you need more information: here, here and here.
 A flaw in a beta version of Facebook made it possible to see member birth dates, even those set to hide this information. Birth dates are often used to confirm someone’s identity. By having a full name and birth date it’s possible to phone up companies and ask for more private information (this is called Identity Theft).
A flaw in a beta version of Facebook made it possible to see member birth dates, even those set to hide this information. Birth dates are often used to confirm someone’s identity. By having a full name and birth date it’s possible to phone up companies and ask for more private information (this is called Identity Theft). They can’t track your name or phone number using this, but they can work out your shopping habits such as which shops you walk into. If they were extra smart they would link your name, when you pay for something with a credit card, to your phone’s ID. But they haven’t done this yet.
They can’t track your name or phone number using this, but they can work out your shopping habits such as which shops you walk into. If they were extra smart they would link your name, when you pay for something with a credit card, to your phone’s ID. But they haven’t done this yet. That’s a lot of information recorded on the actual ticket itself. Usually tickets just have a serial number, or sometimes even a person’s name.
That’s a lot of information recorded on the actual ticket itself. Usually tickets just have a serial number, or sometimes even a person’s name. A flaw has been discovered that can allow web site creators to know if you’ve been to a particular site.
A flaw has been discovered that can allow web site creators to know if you’ve been to a particular site.  Gregory Kopiloff, from Seattle USA, has pleaded guilty to a number of fraud related crimes and has been jailed for 4 years. He used LimeWire to download tax and credit reports, bank statements and student financial aid applications that people had made available using this P2P system.
Gregory Kopiloff, from Seattle USA, has pleaded guilty to a number of fraud related crimes and has been jailed for 4 years. He used LimeWire to download tax and credit reports, bank statements and student financial aid applications that people had made available using this P2P system.  G-Archiver costs US$29.95, and it does what it claims. To use it you enter your Gmail username and password, and it downloads emails to your computer as a backup.
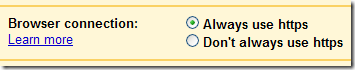
G-Archiver costs US$29.95, and it does what it claims. To use it you enter your Gmail username and password, and it downloads emails to your computer as a backup. A5 encryption was always a weak design but the equipment to decode it used to cost between US$70,000 and US$500,000 so it wasn’t very common.
A5 encryption was always a weak design but the equipment to decode it used to cost between US$70,000 and US$500,000 so it wasn’t very common.