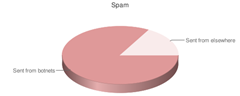
The technology spammers use is always changing. A report released by MessageLabs in June 2009 shows that 83% of spam is currently being sent from botnets. Now let’s explain what a botnet is.
There are people out there who hack into people’s home PCs (the PCs of ordinary people like you and me). They usually write a virus to do this, or pay someone to write the virus. Then when they’ve hacked into a home PC, they add it to a list.
After a few days they can get about 500,000 home computers on their list (yes, they work very fast). So once the hacker has hundreds of thousands of computers on their list, he writes a program that can control them all at once.
Now keep in mind that most home users won’t know their PC has been hacked. Everything still looks normal.
The hacker then sells this list of PCs to a spammer. The technical word for this list of controlled PCs is called a botnet.
A spammer buys this list of hacked computers and the program that controls them all at once. He uses also buys an email list from someone else (a list with millions of people’s email addresses). He presses a button, and all of the home PCs he’s controlling start sending out spam.
Again, home users don’t know their PC is now being used to send out spam. They might notice their internet go a little slower but most people don’t have the technical skill to work out why. It just gets ignored.
The spammer then sits back, relaxes after doing his 5 minutes of work. If anyone gets caught for sending spam it’ll be the home user, not him. The home user is ignorant of what’s going on. The hacker made his money and will do it again. And the cycle repeats again after a few days.
 So how much spam are we talking about?
So how much spam are we talking about?
The largest botnet in operation in June 2009 is sending 74 million spam emails a day, all of this from people’s home computers. That’s a lot of spam.
What can you do?
Don’t let your own computer become part of a botnet. Use a good antivirus product, scan for malware, and fix up any problems.
Too bad the hackers and spammers
are getting away with this nonsense.
Thanks for sharing. I’m going to get
mine checked.