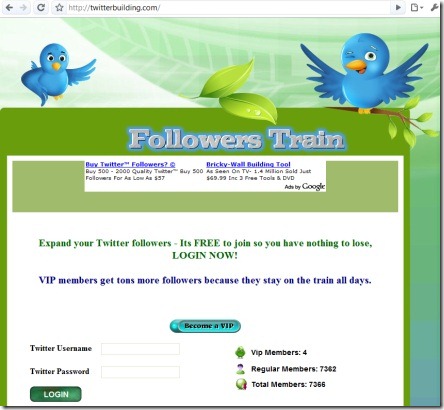
Twitterbuilding (dot com) is a web site that promises a few Twitter features. It’s a fake site. It steals people’s Twitter account details. Do not use the Twitterbuilding site.
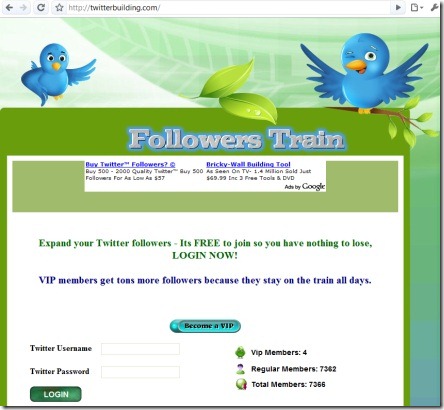
Twitterbuilding (dot com) is a web site that promises a few Twitter features. It’s a fake site. It steals people’s Twitter account details. Do not use the Twitterbuilding site.
Android is a system used by some smartphones (similar to iPhone or Windows Mobile, but made by Google). Like other smartphones you can install apps on Android.
One Android app that showed up recently is a free banking app. It looks like it supports US banks. But instead of logging into your bank it sends your online banking details to a scammer. Then it won’t be long until someone steals money from your bank account.
Google has been notified of this malicious app and they have removed it. But for some people it may be too late.
There’s a lesson to be learnt here. Smartphones are cool, installing apps on them is cool. But we shouldn’t let our guard down and trust everything to them. Know what you’re installing, know who wrote the software, and how it stores and sends your login details.
As more people buy smartphone scams are only going to become more common.
I just received the following email. It’s a scam made to look like Google Adwords, however the web site was registered just a few hours ago to somebody else.
If you go to this site and enter your Google account details you’re actually letting a stranger (hacker) know your account details. It’s a scam.
———————————————
This message was sent from a notification-only email address that does
not accept incoming email. Please do not reply to this message.
Message id:388520237785520
———————————————Hello,
You have a new text alert from adwords
Please use the link below to login:
http://www.adwlordls.com/Selects/Login/static/index.html?ref=56105007342
Advertise your business on Google
Best regards, Google AdWords Customer Team © 2009
———————————————
This message was sent from a notification-only email address that does
not accept incoming email. Please do not reply to this message.
Message id:847914946168909
———————————————
So if you see this email or one like it, delete it. Google did not send this email.
Update: another version of this scam is,
This message was sent from a notification-only email address that does
not accept incoming email. Please do not reply to this message. If you
have any questions, please our Help Center to find answers to
frequently asked questions.
————————Hello,
Please update your primary and backup payment information, even if you
plan to use the same information. Please follow the steps
below to update your information and trigger our billing system to try
processing your payment again. We’ll attempt to process your balance on
whichever card you update first.1. Log in to your AdWords account at <link removed>
2. Enter your new or updated payment information.
3. Click ‘Save Changes’ when you are finished.To update your backup credit card:
1. Visit the ‘Billing Preferences’ page, as described above.
2. In the Backup Credit Card section, click ‘Edit’.
3. Re-enter your backup credit card details.
4. Click ‘Save’.To update your bank account:
1. Visit the ‘Billing Preferences’ page, as described above.
2. In the Bank Account section, click ‘Edit’.
3. Re-enter your bank account details.
4. Click ‘Save’.Thank you for advertising with GoogIe AdWords.
Grow your business with us.Sincerely,
The GoogIe AdWords Team
If you see this email delete it, don’t click on the link, don’t give them your Google password.
And yet another version:
Dear Valued Customer,
You have a new alert from Google Adwords.
Sign in to your AdWords account at http://adwords.googlxmcn.com/
Select/login Yours Sincerely,
The AdWords Team
Notice the domain name above, googlxmcn.com. This is not google.com, it’s spelt differently, so it’s a scam.
This product is a scam. It’s made to look like a real antivirus or antispyware program but all it does is ask you for money. It’s not a legitimate program, it doesn’t stop spyware, viruses or do anything useful.
It’s called PC Antispyware 2010, a name that sounds a bit serious (and misleading). The screen looks pretty fancy, maybe people trust things that look nice or shiny – don’t be fooled by it.
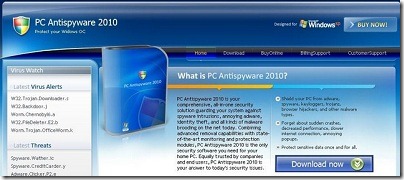
If you see the screen above then don’t click on the download link, don’t install it. You can see a larger screenshot by clicking here. Only use antivirus products from known and trusted vendors.
Accounts are often hacked, including Facebook accounts. Too many times people fall for scam emails telling them to (urgently) click on a link and type in their password. Too many times people don’t know how to tell the difference between the real Facebook login page and one made by a scammer (read here for some hints).
And when an account does become compromised and hacked, the scammers usually use it to send out spam. Then it can be difficult for people like you to get that account back.
Facebook has given this problem some thought and added a way to recover a compromised account. They will send you an email and ask you to verify your account. Then on their web site they’ll ask you some security questions and ask you to change your password.
There’s more info here.
This one’s an old phishing email that never gives up, it’s still being sent in bulk to just about everyone.
St George is an Australian bank and this email’s designed to catch out their customers and to steal their online banking details.
Below is a copy of the email:
Restore your Internet Banking Access
As a result of too many incorrect attempts to access Internet Banking, your access to this service has been locked. We apologize for any inconvenience this may cause.
Please logon to your account and restore your access as soon as possible.
Internet Banking: Restore Access
 Like all phishing attempts it’s designed to strike some fear and sense of urgency into account holders. Fear and urgency often cause people to make irrational decisions, and possibly to click on the link and quickly type in their banking details before realising they’re on a fake site.
Like all phishing attempts it’s designed to strike some fear and sense of urgency into account holders. Fear and urgency often cause people to make irrational decisions, and possibly to click on the link and quickly type in their banking details before realising they’re on a fake site.
Because this email’s been around for some time a lot of web browsers, email clients, and anti-virus products will block it. If it hasn’t been blocked on your system then you really need to upgrade your software.
 A new phishing email designed to catch PayPal users. This one should be fairly easy to identify as a phishing attempt, the “story” in the email doesn’t make much sense at all. It just mentions PayPal and that you need to open an attachment.
A new phishing email designed to catch PayPal users. This one should be fairly easy to identify as a phishing attempt, the “story” in the email doesn’t make much sense at all. It just mentions PayPal and that you need to open an attachment.
Here’s the email:
For security reasons we have sent you this message as an attachment file. This measure has been adopted to prevent personal information theft and data loss. Please do not reply to this e-mail. Mail sent to this address cannot be answered. For assistance, log in to your PayPal account and choose the "Help" link in the footer of any page. To receive email notifications in plain text instead of HTML,update your preferences.
PayPal Email ID PP694
If you see this just delete it. Don’t open the attachment and certainly don’t type your PayPal login details onto the web page it sends you to.
Citi Prepaid Services is a legitimate banking service. Recently some emails have been sent that look like they came from this service. Like most phishing attacks it contains an email that tries to scare you into clicking their link.
The link takes you to a web page that “looks like” Citi Prepaid Services, however it’s run by hackers and used to collect your login details (this is called phishing).
Below is the scam email:
Dear Ecount Citi Prepaid Services Member,
Due to concerns, for safety and integrity of the online banking community we have issues this warning message.
It has come to our attention that your account information needs to be updated due to inactive members, frauds and spoof reports. If you could take 5 – 10 minutes out of your online experience, and renew your records you will not run into future problems with the online service.
NOTE: THIS NOTIFICATION EXPIRES ON MAY 17, 2009.
Once you have updated your account records, your internet banking service will not be interrupted and will continue as normal.
Please click the link bellow and renew your account information
Scammers obviously have terrible English skills (though they’ve gotten better in the last couple of years). The email shown above has at least 2 grammatical errors and at least 1 spelling error. Maybe they should spend some of that stolen money to pay for better education.
Even if you’re not a customer of the service above, this serves as a reminder that scammers never give up sending out these phishing emails. Always be wary of emails that try to scare or shock you into clicking a link.
Instead of clicking on their link, open a new web browser and type in your bank’s web site. Trust your own memory (or better yet a bookmark) rather than an unsolicited email.
You can also use a good anti-virus package that scans web pages for scams such as this one. And modern web browsers such as Chrome can also filter out some scams as well, so keep upgrading your browsers.
There’s a message being sent on Twitter that tells people they can add 1000 followers in one go. The message has a link to a website called twittercut [dot] com.
Don’t click on this site, it asks you for your Twitter account name and password. If you were to hand over your Twitter account details it then sends the same message from your account.
Always be very careful when handing over your account details to unknown web sites.